Visitor management in healthcare has evolved from a sign-in clipboard at the nursing station to a sophisticated digital infrastructure that screens, credentials, tracks, and directs visitors throughout the hospital campus. The drivers of this evolution are simultaneously clinical (infection control), regulatory (Joint Commission security management), and reputational (patient safety events involving unauthorized visitors).
For healthcare facility directors and security managers, implementing an effective visitor management system requires understanding both the technology options and the operational integration required to make them work.
Why Hospital Visitor Management Is Complex
Unlike corporate offices where visitors are relatively predictable and the risk profile is manageable, hospitals host an extraordinarily diverse visitor population with dramatically varying risk profiles:
- Family members and friends visiting inpatients
- Contractors and vendors delivering goods or performing maintenance
- Pharmaceutical and device sales representatives
- Clergy and chaplaincy volunteers
- Legal representatives and social workers
- Law enforcement
- Media and communications staff
- Students and clinical observers
Each category has different access needs, different screening requirements, and different duration of stay. A visitor management system that applies a single process to all categories will either be too burdensome for routine visitors or insufficiently rigorous for higher-risk categories.
Core Screening Functions
Modern healthcare visitor management systems integrate several screening capabilities:
Photo ID scan and capture — Visitors present a government-issued photo ID that is scanned and captured. The system retains the image for audit purposes and extracts demographic information to populate the visitor record.
Sex offender registry check — The scanned ID is matched against national sex offender databases. Pediatric facilities, psychiatric units, and facilities serving vulnerable populations should run this check universally. A match generates an alert for security review before the visitor is admitted.
Watchlist screening — Custom internal watchlists allow facilities to flag specific individuals based on prior incidents, court orders, or behavioral history. Security staff are alerted rather than the system automatically denying access.
Healthcare-specific exclusions — Some facilities maintain lists of individuals who have been banned from the campus due to threatening behavior, domestic violence restraining orders, or patient requests for no-contact.
Vaccination and health screening — During infectious disease outbreaks (including COVID-19), visitor management systems can enforce attestation requirements, document vaccination status, or direct visitors to screening checkpoints before proceeding.
Visitor Badging and Time-Limited Access
Visitor badges serve both identification and access control functions. Modern visitor badges include:
- Photo of the visitor (printed at the kiosk)
- Visitor name and the patient or department they are visiting
- Date and time of issue
- Expiration information (typically end of day)
- Color coding or zone designation for allowed areas
- Barcode or QR code that integrates with the access control system for door access
Badges should be clearly distinct from employee credentials. Color, size, or a “VISITOR” designation visible at a distance helps staff identify visitors in restricted areas. Many facilities use time-expiring paper badges with chemical indicators that change color after a set period, making it obvious when a badge is expired even without electronic verification.
COVID-19 and the Transformation of Visitor Management (2020)
COVID-19 forced healthcare visitor management to undergo radical transformation in weeks. Visitor restriction policies — implemented to reduce COVID-19 transmission risk — shifted visitor management from a welcome function to a screening and gatekeeping function.
The operational requirements during peak restrictions included:
- Designated, controlled entry points (typically one or two campus-wide)
- Active symptom screening with standardized questionnaire
- Temperature check (forehead thermometer or thermal camera)
- Mask issuance for visitors arriving without them
- Documentation of restriction exceptions (designated support persons for labor and delivery, pediatric parents, patients needing behavioral health support)
Visitor management technology vendors responded with COVID-specific modules that integrated digital symptom attestation, mask compliance documentation, and time-limited campus passes.
The pandemic also validated the investment in digital visitor management for many facilities that had previously relied on manual processes. The volume and complexity of visitor screening during COVID-19 would have been operationally impossible without digital infrastructure.
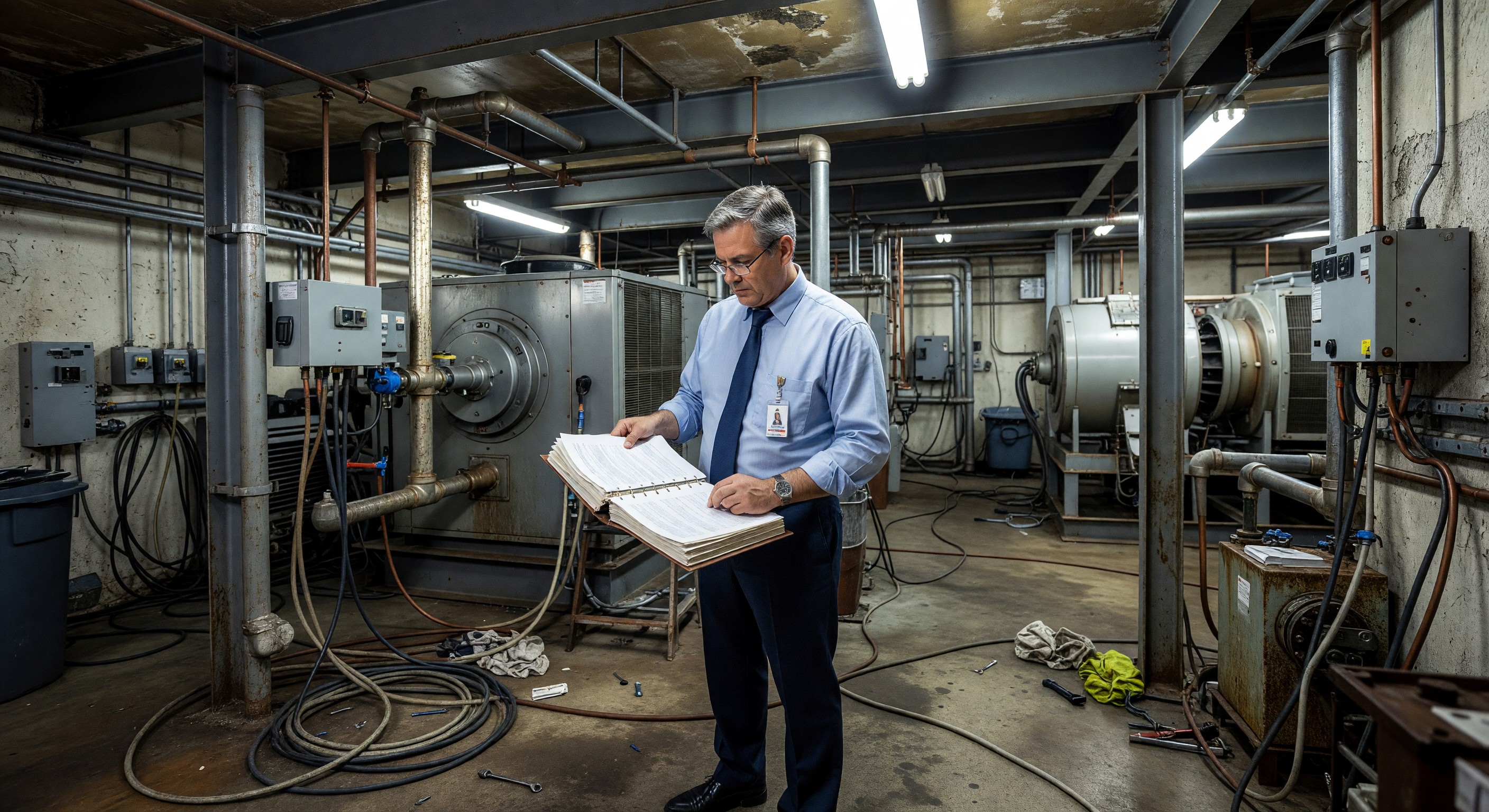
Contractor and Vendor Management
Vendors, contractors, and service representatives require a different visitor management workflow than personal visitors. Key differences:
Credential verification — Contractors should demonstrate insurance, licensing, and required certifications before receiving campus access. Visitor management platforms with contractor modules maintain credential records and alert when certifications expire.
Orientation requirements — Many hospitals require contractors to complete a brief facility-specific safety orientation before working on campus. This can be delivered digitally through the visitor management system before or at check-in.
Escort requirements — Some zones require that contractors be escorted by an authorized staff member. The visitor management system should document escort identity and allow tracking of contractor location during the visit.
Work order integration — Ideally, contractor check-in ties to an active work order, limiting access credentials to the specific areas and time windows associated with the work order.
Integration with Access Control Infrastructure
Visitor management systems reach their full potential when integrated with the facility’s physical access control system. This integration enables:
- Visitor badges to grant limited, time-specific access to defined zones without staff escort
- Automatic expiration of visitor access credentials at end of visit
- Audit trails that combine visitor check-in records with door access event logs
- Denied access alerts if a visitor attempts to enter an unauthorized zone
Integration requires that the visitor management system and access control system share a common data protocol or that a middleware integration layer is deployed. When evaluating visitor management platforms, confirm compatibility with your existing access control system brand and protocol.
Frequently Asked Questions
How long should visitor records be retained? Retain visitor logs for a minimum of one year for general compliance purposes. For records associated with security incidents, retain for seven years or the duration of any related litigation. Healthcare attorney review of your specific record retention policy is advisable.
Should we require visitor management check-in for labor and delivery companions? Yes — but the process should be compassionate and efficient. A patient arriving in active labor cannot wait 10 minutes for her partner to complete a visitor screening process. Pre-register birth companions in advance through the patient portal, and create a fast-track lane at check-in for this category.
How do we handle a visitor who is flagged on the sex offender registry? Have a written policy before you need it. Typically: the system alerts security without displaying the result to the visitor; security assesses the situation privately; a manager makes a determination based on the specific offense, the patient they are visiting, and the unit involved. A blanket denial policy may face legal challenge in some circumstances. Have your legal counsel review the policy.
What is the cost range for implementing a digital visitor management system? Basic digital visitor management (kiosk, ID scanning, badge printing, basic records) ranges from $5,000–$20,000 per location for hardware, plus $3,000–$15,000 annually in software licensing. Enterprise platforms with contractor management, access control integration, and sex offender screening can range from $50,000–$200,000 for a multi-location deployment. Ongoing per-location software costs are typically $5,000–$25,000 annually.